TL;DR: Businesses are no longer relying on cameras alone to protect their facilities. Non-visual sensors such as motion detection, thermal sensors, glass break sensors, gunshot detection, environmental monitoring, and access control alerts are creating an earlier-warning perimeter. These technologies detect unusual activity before a visible security event occurs, giving teams time to verify, communicate, and respond. When integrated into a unified platform, non-visual sensors strengthen layered security by closing gaps that cameras cannot cover alone.
The Perimeter Has Changed
For years, perimeter security meant fencing, lighting, and cameras mounted on the exterior of a building.
Today, threats do not always approach in obvious ways. They may involve after-hours movement, forced entry attempts, temperature anomalies in server rooms, or abnormal sounds before visible damage occurs.
Cameras are powerful. But cameras are reactive. They require something to enter the frame.
Non-visual sensors are shifting the timeline forward.
They detect change before a situation becomes obvious on video.
That shift in timing matters.
What Are Non-Visual Sensors?
Non-visual sensors are devices that detect environmental or physical changes rather than relying on video footage.
Common examples include:
Motion and intrusion detection sensors
Glass break sensors
Door position sensors
Thermal sensors
Gunshot detection systems
Environmental sensors (temperature, humidity, water leaks)
Vibration or impact sensors
These tools operate quietly in the background. They monitor patterns and alert teams when thresholds are crossed.
In many cases, they activate before a person ever appears clearly on camera.
Detecting Threats Before They Escalate
1. Motion Detection Beyond Camera View
Cameras only record what they see.
Motion sensors detect activity in blind spots, low-light conditions, or areas where video may not be continuously monitored.
An after-hours motion alert in a restricted warehouse aisle triggers verification before theft escalates.
2. Thermal Sensors for Early Warning
Thermal sensors detect abnormal heat signatures.
This can indicate:
Electrical panel overheating
Equipment malfunction
Unauthorized presence in dark environments
Fire risks before visible flames
In environments like manufacturing plants, distribution centers, or data rooms, early thermal alerts prevent operational disruption.
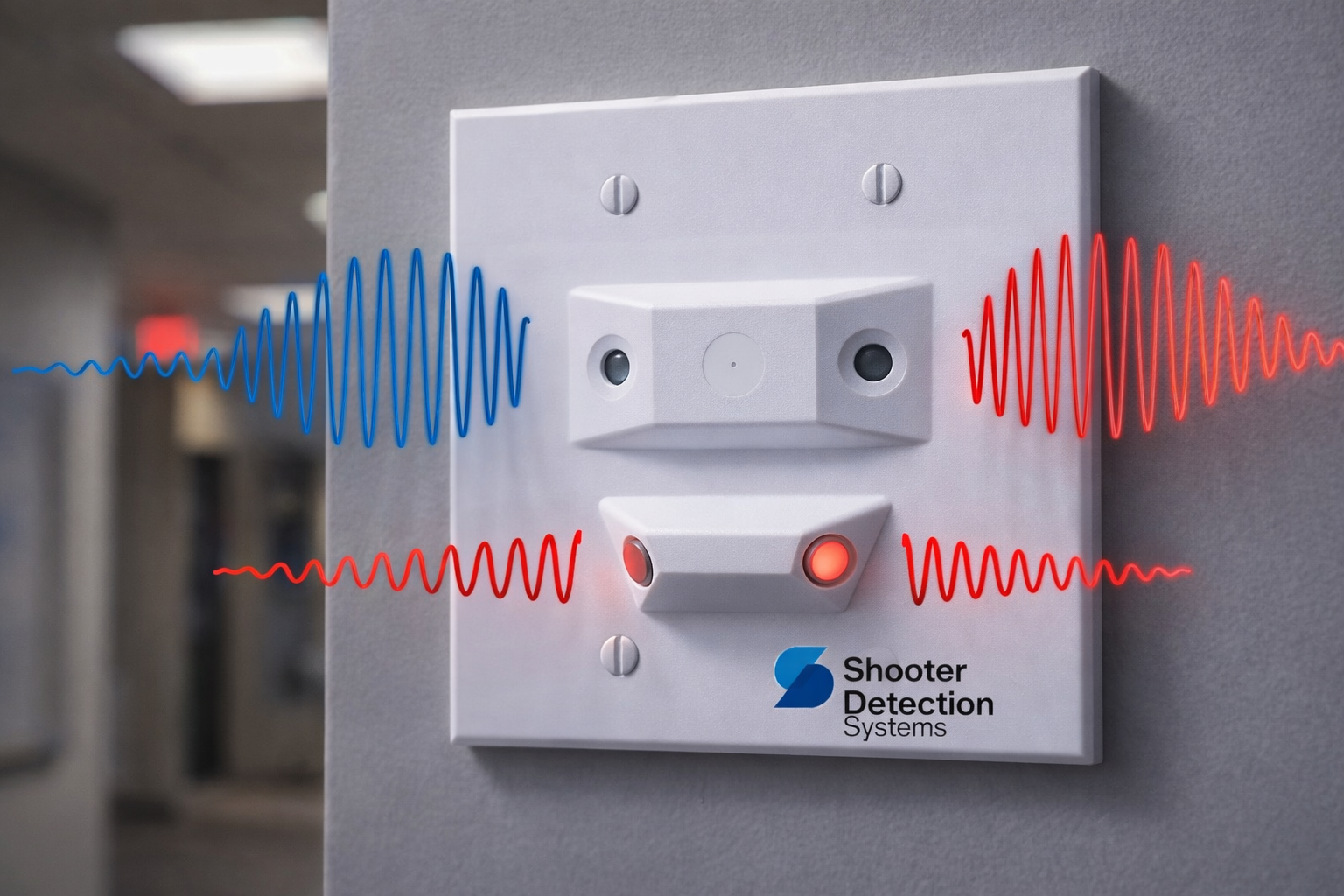
3. Gunshot Detection and Acoustic Monitoring
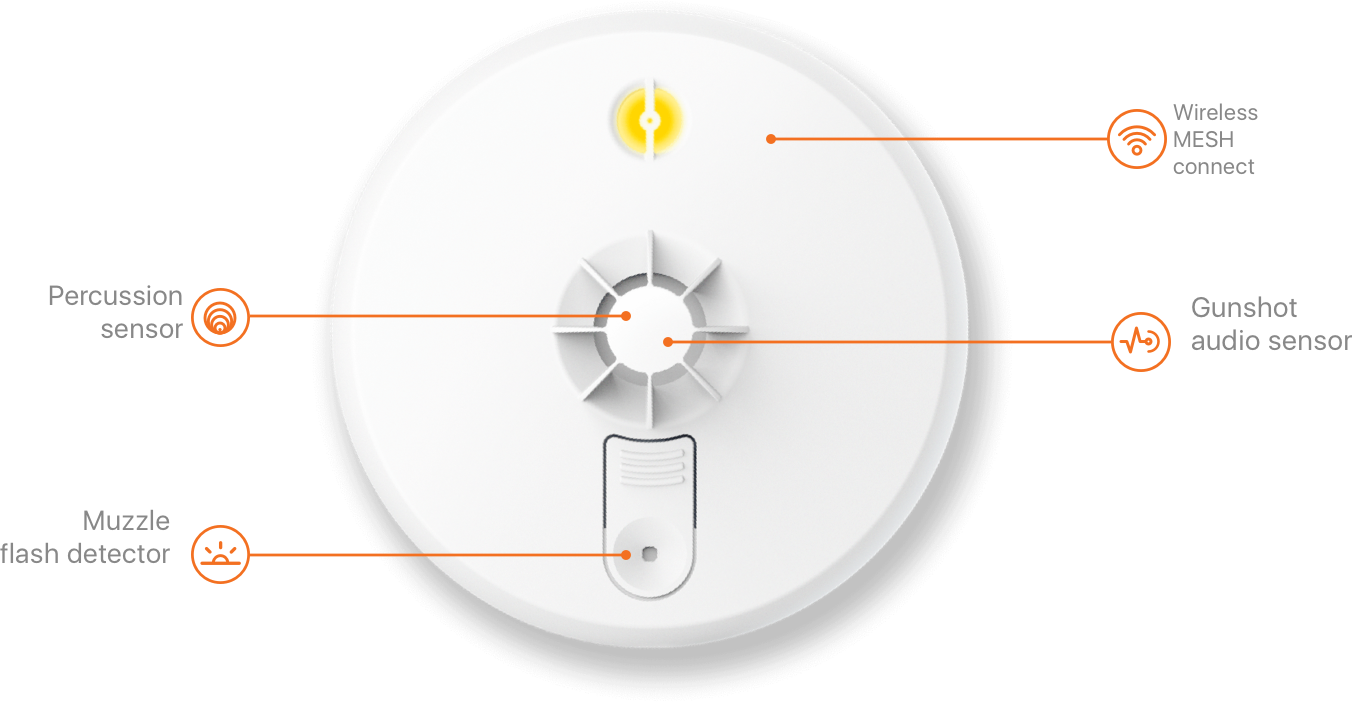
Acoustic sensors analyze sound patterns in real time.
If a gunshot occurs, detection systems can:
Identify the sound signature
Pinpoint the location
Trigger lockdown protocols
Notify first responders immediately
This reduces response time from minutes to seconds.
4. Environmental Monitoring as Risk Prevention
Not every threat is violent.
Water leaks, frozen pipes, HVAC failures, or humidity spikes can cause severe financial damage.
Environmental sensors protect:
Server rooms
Medical storage
Manufacturing equipment
Archive storage areas
These are not headline events. But they are high-cost failures when ignored.
The Power of Integration
The real advantage appears when non-visual sensors integrate with video, access control, and alerting systems.
For example:
A door forced open after hours triggers:
Access control alert
Nearby camera recording
Mobile notification
Optional monitoring center escalation
A temperature spike in an electrical closet triggers:
Maintenance alert
Camera verification
Automated workflow
Platforms like Verkada and Motorola Solutions are leading this unified approach, combining sensors, video, and cloud-based management into a single interface.
Instead of isolated alarms, businesses gain coordinated intelligence.
Why This Matters for Business Leaders
Early detection changes outcomes.
When security systems alert you before visible damage or escalation:
Response becomes proactive instead of reactive
Downtime is minimized
Liability exposure decreases
Safety teams operate with clarity
Insurance conversations improve
This is especially important for:
Manufacturing facilities
Healthcare environments
Schools and Houses of Worship
Multi-site enterprises
Distribution centers
The goal is not more noise.
The goal is smarter signal.
Moving from Cameras to Comprehensive Detection
Cameras remain essential.
But relying on video alone creates blind spots.
Non-visual sensors extend the perimeter beyond what the eye can see. They detect vibration, heat, sound, pressure, motion, and environmental change.
When combined with layered security principles, they create a perimeter that is dynamic instead of static.
A perimeter that listens.
A perimeter that measures.
A perimeter that reacts early.
What to Consider When Implementing Non-Visual Sensors
Identify your highest-risk areas.
Determine where early detection would change the outcome.
Evaluate integration capabilities with your existing platform.
Avoid standalone systems that do not communicate.
Prioritize centralized visibility.
Security technology should reduce complexity, not add it.
See How You Can Integrate Early Detection Technologies into Your Layered Security Strategy
The perimeter is no longer just a physical boundary.
It is a network of intelligent detection points designed to identify risk before it becomes a crisis.
Organizations that adopt non-visual sensors are not replacing cameras. They are strengthening the entire security ecosystem.
If you want to see how early detection technologies integrate into a layered security strategy, schedule a walkthrough of the Hoosier Security Experience Center and explore how detection, analysis, communication, and response work together in real time.